Following large investments in quantum computing followed by the ensuing advancement of this technology in recent years, as well as looking forward to benefits this could bring, there is also the growing threat of ‘quantum hacking’.
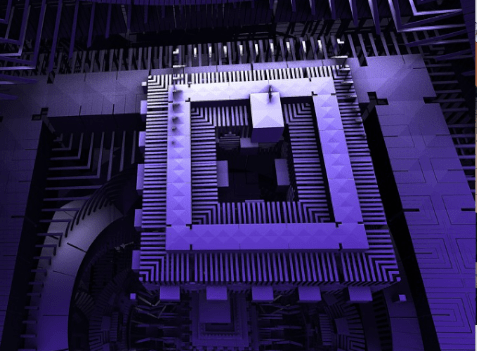
Quantum Computers
Quantum computers can carry out complex calculations at high speed. Whereas traditional computers store data in binary ‘bits’ (ones and zeros) and work by creating and storing long strings of these ‘bits’, quantum computing’s ‘qubits’ (quantum bits) can do both at once. This is because a qubit can hold a zero, a one, or any proportion of both zero and one at the same time, while an array of qubits can use something called ‘superposition’ to represent all 2^64 fewer bits (i.e: much more information can be stored in fewer qubits), therefore information can be processed much more quickly than with a traditional computer. The power of a quantum computer is stated in its quantum volume number / how many qubits, for example, a 14-qubit system.
As a result, quantum computers can be used to dramatically speed up tasks that have traditionally taken a long time, such as finding new drug molecules for example. The results can be astounding, where crunching numbers that would take a classical computer a week, could take a quantum computer less than a second.
The power of quantum technologies offers possible solutions to some of the world’s biggest and most pressing challenges, eg: global warming, healthcare, energy and more.
Investment
Governments and private investors have been pledging and ploughing much more cash into developing quantum computing technology in recent years. For example:
– In March this year, the UK announced it’s ‘National Quantum Strategy’ whereby there will be £2.5 billion investment.
– The US National Quantum Initiative Act was signed into law in 2018, providing over $1.2 billion in funding over 5 years for quantum computing research and development.
– In 2021, investment in quantum R&D reached $1.7bn, which was a 20 times increase from five years previously and US quantum startups raised double ($870m) what they raised in 2020 (McKinsey & Company).
The Threat
Although quantum computers are powerful enough to help solve some of the world’s biggest challenges, this power could also mean that they could soon also pose a threat. For example, quantum computers have the potential to break many of the commonly used encryption schemes that are used today, including RSA and elliptic curve cryptography (ECC). These encryption schemes rely on mathematical problems (such as factoring large numbers or computing discrete logarithms) which are difficult to solve using classical computers but can be solved efficiently using quantum algorithms.
With a powerful enough quantum computer, the risk is that an attacker could use these algorithms to break the encryption keys used to protect sensitive data, such as financial transactions, medical records, and government secrets. This could result in the exposure of confidential information, financial loss, and even threats to national security.
Quantum Hacking Threat
As quantum computing technology advances, some tech and security commentators have warned of the risk of ‘quantum hacking.’ This refers to the use of quantum computing techniques to break cryptographic schemes that are commonly used to protect sensitive information. Quantum hacking takes advantage of the properties of quantum systems, such as superposition and entanglement, to perform certain operations much faster than classical computers can.
In the context of cryptography, quantum hacking means using a quantum computer to perform certain mathematical operations that are difficult or infeasible to perform using classical computers. For example, Shor’s algorithm is a quantum algorithm that can efficiently factor large numbers, which is the basis of many widely used cryptographic schemes. By using Shor’s algorithm on a powerful enough quantum computer, an attacker could break the encryption keys used to protect sensitive data.
Quantum hacking also includes attacks that exploit vulnerabilities in quantum communication systems, such as quantum key distribution (QKD). QKD is a method for securely distributing cryptographic keys using quantum properties, but it is vulnerable to certain types of attacks, such as photon number splitting attacks, which can be carried out using quantum technology.
There are also reports that cyber criminals now steal encrypted data in the hope that the encryption can be cracked at a later date, perhaps using quantum computers (‘harvest now, decrypt later’ attacks).
As quantum computing technology continues to advance, the risk of quantum hacking increases, highlighting the need for new cryptographic schemes that are resistant to attacks by quantum computers, known as post-quantum cryptography.
What Is Post-Quantum Cryptography And How Could It Help?
Post-quantum cryptography refers to cryptographic algorithms that are designed to resist attacks by quantum computers. As outlined, quantum computers have the potential to break many of the widely used cryptographic schemes in use today.
Post-quantum cryptography includes a variety of cryptographic algorithms that are based on different mathematical problems that are believed to be hard – even for quantum computers. Examples include lattice-based cryptography, code-based cryptography, hash-based cryptography, and multivariate cryptography, among others.
The goal of post-quantum cryptography is to provide a long-term security solution that can withstand the potential emergence of powerful quantum computers. While quantum computers are still in their early stages of development, research in post-quantum cryptography is ongoing to ensure that secure cryptographic algorithms will be available when the time comes that they are needed.
Public-Key Algorithms
Public-key algorithms are thought to be particularly vulnerable to the quantum hacking threat. For example, the US National Cybersecurity Center of Excellence (NCCoE) has recently highlighted how once access to practical quantum computers becomes available, all public-key algorithms and associated protocols will be vulnerable to criminals, competitors, and other adversaries. The advice is, therefore, that “It is critical to begin planning for the replacement of hardware, software, and services that use public-key algorithms now so that information is protected from future attacks.”
What Does This Mean For Your Business?
Quantum computers offer the chance to solve complex problems and save vast amounts of time in doing so. Not only could quantum computers help with challenges such as developing new medicines, helping find solutions in the climate crisis, and making many other dramatic scientific discoveries, they could also help solve problems in a variety of more mundane industries. For example, quantum computers could be used to optimise supply chains or model financial data in new ways. However, with huge investment and advancement in quantum technologies that could help businesses and humanity comes the risk that they could also be used to crack encryption, leading to the theft and exposure of confidential information, financial loss, and threats to national security. Ways to counter the threat of quantum hacking include advancing and investing more in and implementing post-quantum cryptography, alongside the replacement of hardware, software, and services that use public-key algorithms. Other ways that businesses could protect themselves from the threat of quantum hacking include:
– Monitoring developments in quantum computing and quantum communication technology and staying informed of new attacks and vulnerabilities as they emerge so that appropriate steps can be taken to mitigate these risks.
– Using secure communication protocols, such as Transport Layer Security (TLS), and implementing proper key management practices to protect sensitive data in transit.
– Upgrading encryption algorithms to those that are believed to be resistant to attacks by classical computers.
By Mike Knight
